The Russia-based notorious ransomware gang REvil, which faced plenty of heat following a string of high-profile attacks on JBS and Kaseya, was disrupted by a multi-country law enforcement operation for a second time, as governments around the world continue to tighten the screws on the profitable criminal scheme.

“The REvil ransomware gang restored the infrastructure from the backups under the assumption that they had not been compromised,” Group-IB’s Oleg Skulkin was quoted as saying to Reuters, which reported the development. “Ironically, the gang’s own favorite tactic of compromising the backups was turned against them.”
The shutdown comes weeks after the syndicate re-emerged following a months-long hiatus, during which the group went quiet after attracting scrutiny from the U.S. government in response to its attack on Kaseya, which resulted in thousands of companies becoming infected with ransomware.
What’s trending in security?
❌ Cybersecurity experts have hit out at Apple and the European Union for their push to monitor people’s phones for illicit child sexual abuse material. The experts say that such client-side scanning would embolden state surveillance. [The New York Times]
🇨🇳 The central government of China has announced a decision to allow foreign entities to invest in the ownership of VPN (virtual private network) services in the country. Under this new policy, foreign investors can only own up to 50% of China-based VPN companies. VPN services have been widely used by corporations operating in the country to skirt the Great Firewall and connect to overseas servers. [SCMP]
🕹️ Threat actors are increasingly abusing digital communication platform Discord, a platform with 150 million users, to persistently deliver multi-functional malware—in particular remote access trojans (RATs) that can take over systems. [RiskIQ / Check Point Research]
🛡️ New research has shown that while major ransomware gangs tend to operate outside the Commonwealth of Independent States (CIS), countries in the region are being targeted by dozens of lesser-known cybercriminal groups. According to Russian cybersecurity firm Kaspersky, over 2,000 business users in the CIS have consistently encountered ransomware each month since the start of year. [Kaspersky]
💲 The criminal group FIN7 has once again gone to great lengths by setting up a new fake company called Bastion Secure to recruit unwitting software engineers into a possible ransomware scheme. Not only does the company claims to provide penetration testing services for private companies and public sector organizations, to give the campaign a ring of verisimilitude, one of the the firm’s office addresses has been lifted from a real but now-shuttered office for a U.K.-based firm called Bastion Security (North) Limited. [The Hacker News]
⚠️ Academics from universities in China, Singapore, and Switzerland have discovered a new attack method called “SmashEx” that can break the sanctity of Intel SGX enclaves and steal confidential data from inside an Intel CPU’s most secure area. The attack enables hostile software running on the operating system to abuse a feature that allows the CPU to pause SGX operations to enter the enclave and steal data. Both Intel and Open Enclave have released patches. [The Hacker News]
📺 A new widespread malware campaign has been found creating YouTube videos about software cracks, licenses, and game cheats to host links to file-sharing websites that distribute password-stealing trojans to unsuspecting viewers. [Bleeping Computer]
🛡️ Over 25% of malicious JavaScript code is obfuscated by so-called ‘packers,’ a software packaging method that has given attackers a way of evading signature-based detection. The research is yet another indication that JavaScript obfuscation continues to be a favored method among cyberattackers for sneaking past defenses to deliver a broad range of payloads. [Akamai]


0️⃣ Exploit broker Zerodium is now seeking to buy zero-days in ExpressVPN, NordVPN, and Surfshark's PC apps, namely those that could lead to remote code execution, IP address leak, and other information disclosure. [The Record]
⚡ The Netherlands Forensic Institute, the Dutch government's forensics labs, said it's broken into electric carmaker Tesla's encrypted driving data-storage system, allowing access to a wealth of sensitive information that could be used to investigate crashes. [NFI]
🇦🇫 A new phishing campaign targeting Afghanistan and India has been found utilizing malicious RTF documents to deliver a variety of commodity remote access trojans, such as DcRAT and QuasarRAT. [Cisco Talos]
🇮🇳 The Indian Government’s Power Ministry and the Central Electricity Authority (CEA) released cybersecurity guidelines to enhance the power sector’s cybersecurity readiness. It is the first time that cybersecurity guidelines have been created for the sector. “The guideline lays down required actions for cyber security preparedness across various utilities in power sector so as to raise the level of cyber security preparedness for power sector," the government said. [Press Information Bureau of India]
🌏 A previously unknown state-sponsored actor known as Harvester is deploying a combination of custom and publicly available tools in attacks targeting governments, telecommunication providers, and IT firms in South Asia, with a particular focus on Afghanistan, since at least June 2021. [Symantec]
🗄️ The past two weeks in data breaches, leaks, and ransomware: Accenture, Acer, Atento, Ferrara Candy Co., Meliá, Argentina’s National Registry of Persons, Olympus, Pacific City Bank, Porto Seguro, Quickfox, SCUF Gaming International, Italy’s Società Italiana degli Autori ed Editori, Thingiverse, University of Sunderland, and Verizon’s Visible.
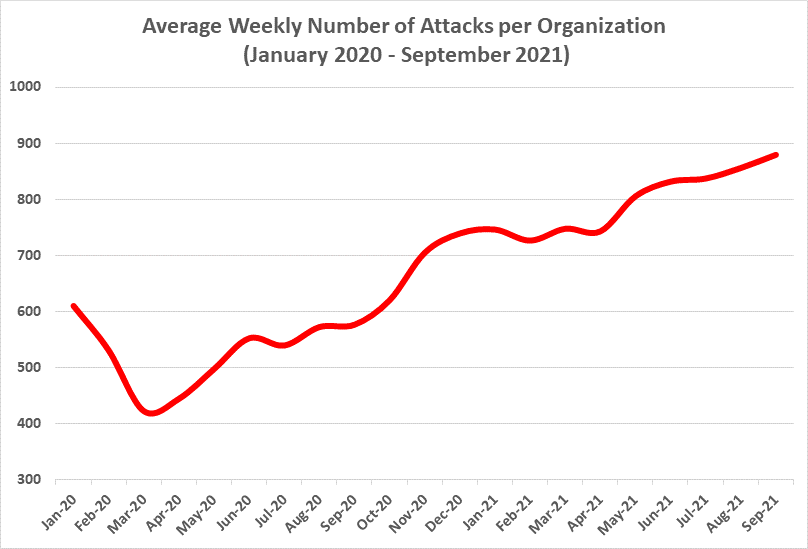
870
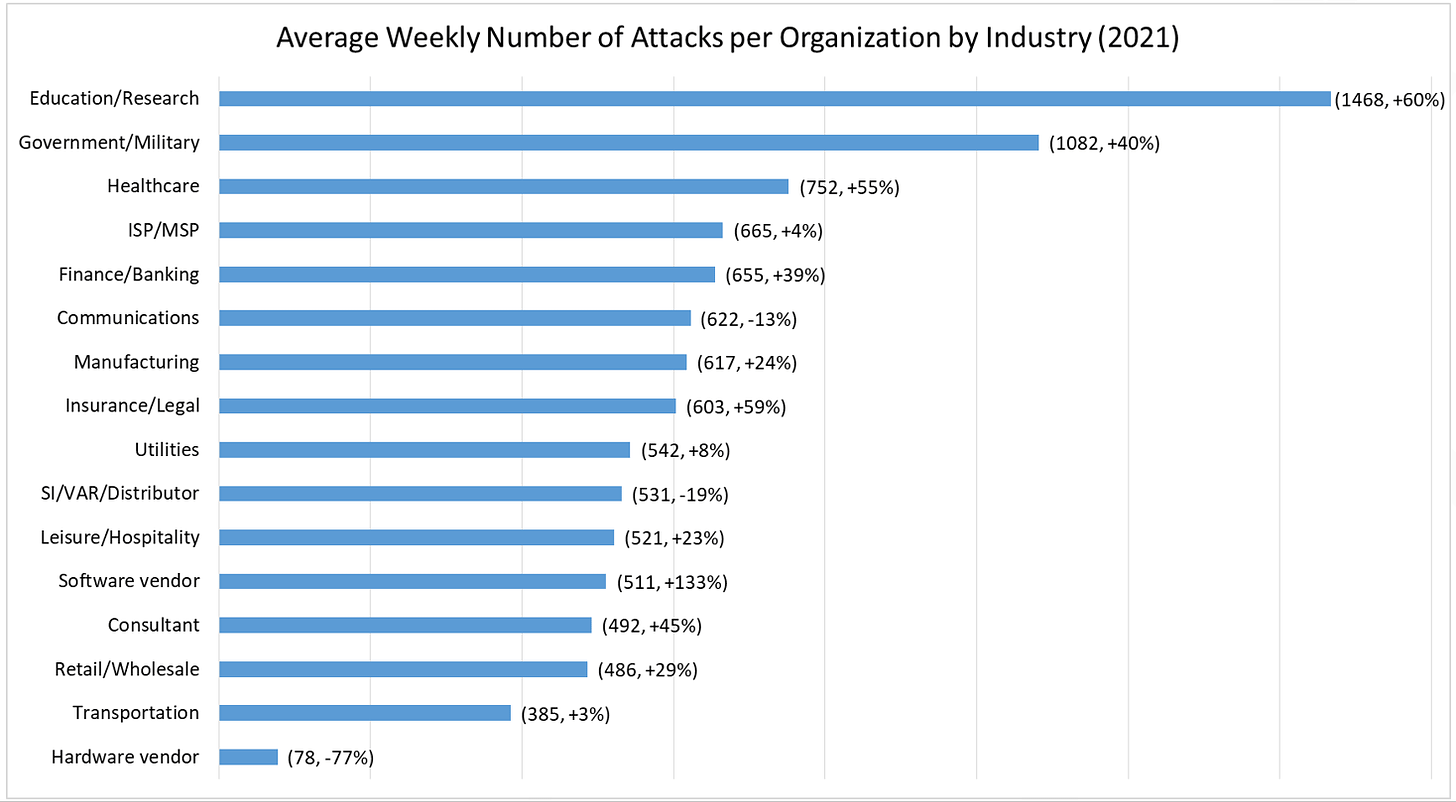
That’s the average weekly number of attacks on each organization globally for the month of September 2021, with education, government, and healthcare sectors targeted the most, according to data compiled by Check Point Research. It’s more than double the number of attacks in March 2020.
Tips, Comments, Ideas?
Send them my way by writing replying to this email.
Thanks again for reading. See you in the next edition!